I was waffling around on GitHub, looking at skidware and I came across something... interesting. I'm not going to deeply document my reverse engineering but if anyone is curious or wants more information, just reach out.
The Repos
The "fudcrypter" topic on GitHub yielded some interesting results. Specifically, four repositories employing the same compromise technique and an additional repository that looks like an old test run of sorts that hasn't been updated since January 31st.
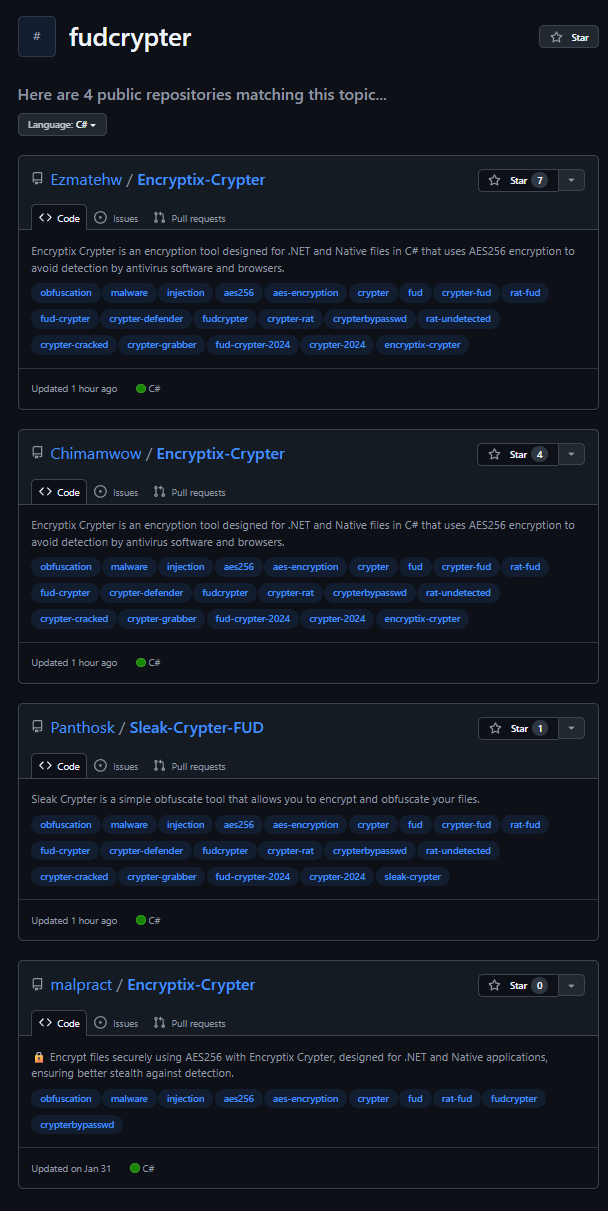
The repository links:
https://github.com/Ezmatehw/Encryptix-Crypterhttps://github.com/Chimamwow/Encryptix-Crypterhttps://github.com/Panthosk/Sleak-Crypter-FUDhttps://github.com/malpract/Encryptix-Crypter
Notice the "Updated 1 hour ago" piece on all three repositories.
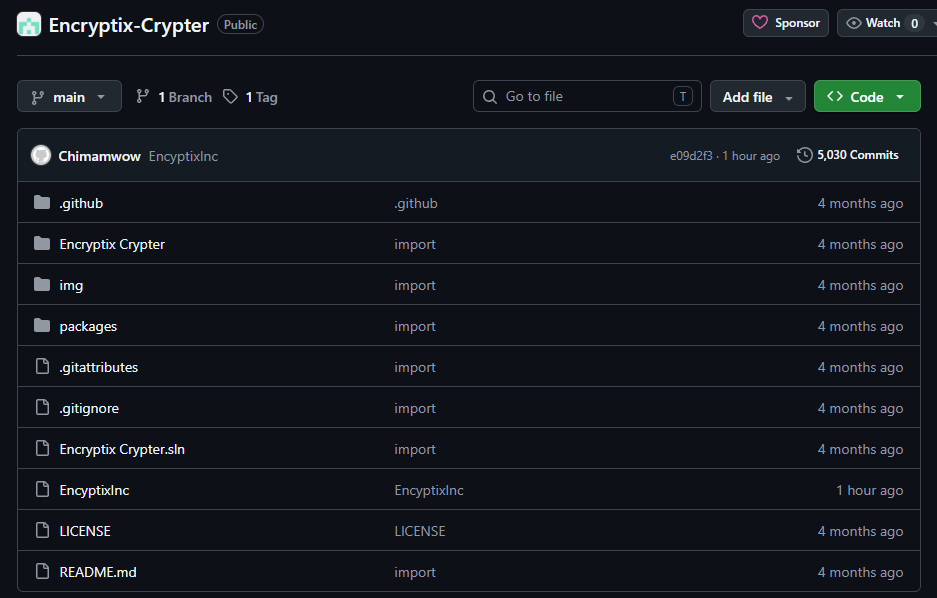
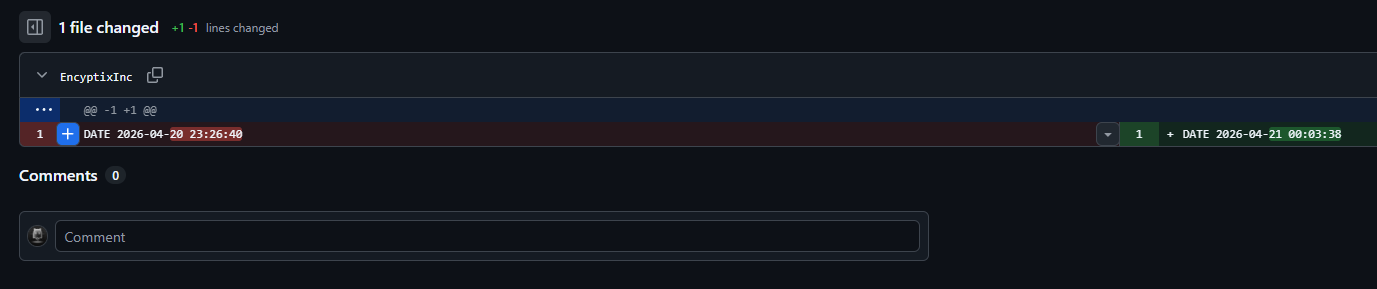
Approximately every hour, each repository has a "timer file" which is incremented.
The Malware
I wasn't born yesterday, so my mind was immediately drawn to the .csproj file. Sure enough, alllll the way at the bottom we find this big ass <PreBuildEvent> element which executes before every build. You can find the VT entry for the file here: https://www.virustotal.com/gui/file/45da1a233b1c87d5612342ef175544411138e9aa96dcbacf3ad356cd08e8308d
Each repository holds the same element to execute before build, but each is slightly different.
Attack Chain Overview
Stage 0
PreBuildEvent in the .csproj file is executed on dotnet build, firing the embedded cmd.exe command.
Stage 1
Inline batch script dropper writes and executes a *********.vbs file via cscript into the %TEMP% folder.
Stage 2
VBScript dropper decodes several base64 chunks and launches a reconstructed stage 3 PowerShell PS1.
Stage 3
This uses AES-256-CBC to decrypt and execute stage 4.
Stage 4
The C2 is contacted, 7z is downloaded, and the final payload installs SearchFilter.exe.
SearchFilter.exe
This little twit is a packaged Node.js file which contains one giant string of Javascript skiddery, primarily performing some anti-analysis items, looks for whether or not the user is an admin, runs some extra PowerShell, and communicates with Telegram using these two URLs. Do with them what you wish.
https://api.telegram.org/bot8401633675:AAGwUsjoFdufyMVUcklGcq_6wwvqSTX31jo/sendMessagehttps://api.telegram.org/bot8401633675:AAGwUsjoFdufyMVUcklGcq_6wwvqSTX31jo/sendPhoto
Channel ID: -1003185977222
The executable is full of crap but you can rip out the ASAR and see the actual main.js file that holds the skiddery activity. It's a bit of a bitch to reverse, but it's doable with the assistance of an LLM if you value speed over hand analysis.
The IoCs
In my analysis, I came across a four-tier C2 fallback chain.
SearchHost.exe
https://www.virustotal.com/gui/file/5f337e059dfa2e23d1c631f636e5f61b59163919d80d9a5798a60bdfd6d03165
SHA256: 5f337e059dfa2e23d1c631f636e5f61b59163919d80d9a5798a60bdfd6d03165
Vhash: 0180a6656d55161d1d1654z23zff3z12z143za7z3001f334zb0c
Contains: https://www.virustotal.com/gui/file/95972ee11d276af5686fd5a5c31bf7ac4ecc8137aed2c5831119e1958163db62
Primary C2
https://rlim[.]com/seraswodinsx/raw
Contains:
w5nDpMOWwqnCn3JifMKfw5fCtMOmw7DDhMKPwp7DhsKRW8K/wr7Dh8Kxwod4wpFkf2vCncK3w6PDncKUwpDCrcK8wpDCkcOew6TDlcOVaMKQwqfCqsK7wqTDncKhw6LCqsOZw4bCncKJU3/DosOSw6LDhcKhcsKhwp/DgcKdw6BuwrXDtQ==
Which decrypts to:
https://github.com/BMWONLY123/web2/releases/download/web2/SearchFilter.7z
Secondary C2
https://codesandbox[.]io/embed/qdy6j9?view=preview&module=%2Fdart
Contains: w5nDpMOWwqnCn3JifMKfw5fCtMOmw7DDhMKPwp7DhsKRW8K/wr7Dh8Kxwod4wpFkf2vCncK3w6PDncKUwpDCrcK8wpDCkcOew6TDlcOVaMKQwqfCqsK7wqTDncKhw6LCqsOZw4bCncKJU3/DosOSw6LDhcKhcsKhwp/DgcKdw6BuwrXDtQ==.deodorantkindredimpo
Which decrypts to:
https://github.com/BMWONLY123/web2/releases/download/web2/SearchFilter.7z
Third C2
https://youtu[.]be/XiH4D4UguJA
Contains:
w5nDpMOWwqnCn3JifMKfw5fCtMOmw7DDhMKPwp7DhsKRW8K/wr7Dh8Kxwod4wpFkf2vCncK3w6PDncKUwpDCrcK8wpDCkcOew6TDlcOVaMKQwqfCqsK7wqTDncKhw6LCqsOZw4bCncKJU3/DosOSw6LDhcKhcsKhwp/DgcKdw6BuwrXDtQ==.deodorantkindredimpo
Which decrypts to:
https://github.com/BMWONLY123/web2/releases/download/web2/SearchFilter.7z
Fourth C2
https://docs.google[.]com/document/d/19ljVCOs-lyGxXbM4V1fSI5_svRuBcfqRDBh39eQlA8w/edit?usp=sharing
* Terminated for ToS violation.
C2 Notes
Tiers 2–4 use a dead-drop resolver pattern. Rather than hosting the payload URL directly, the C2 page contains an encrypted string embedded within otherwise innocuous content. The payload extracts it using the regex:
([a-zA-Z0-9+/=]{50,})\.deodorantkindredimpo
The matched Base64 string is then decrypted with the $proc Vigenère key to yield the actual download URL. This technique makes the C2 infrastructure look like legitimate web content to network monitoring tools, and allows the attacker to update the payload URL by simply editing the host page.
Tier 1 (rlim.com) uses a direct mode (-if): the page content itself is the encrypted download URL, decoded directly without the regex extraction step.
The Artifacts
I had Claude put together a Jupyter notebook that runs through everything. You just need to provide it with the .csproj file and it'll do its thing.
Jupyter here